Executive Summary
Previously, the IAS Threat Lab published research on Arcade, a mobile ad fraud scheme in which mobile apps generated hidden in-app browser activity to load websites in the background and convert mobile-origin activity into web traffic.
Following the publication of Arcade, the IAS Threat Lab continued to monitor related activity across mobile apps and web infrastructure. As this monitoring continued, new traffic patterns and domain behaviors emerged that were not consistent with earlier infrastructure. These changes led to the identification of a distinct operation, now referred to as Genisys.
At this scale, the fraud was embedded directly within everyday smartphones and tablets across multiple markets. Devices were hijacked to run malicious activity in the background, diverting processing power and network resources without users’ knowledge or consent and without delivering any legitimate user benefit.
These apps interface with a network of nearly 500 AI-generated domains. Unlike earlier iterations of this scheme, most of these domains were created using AI-generated tools. They appear as generic blogs, news-style sites, and informational properties produced at scale, built not to attract real audiences but to receive and monetize fraudulent traffic. Collectively, they form a synthetic web ecosystem designed specifically to launder app generated activity into seemingly legitimate web inventory.
IAS Threat Lab worked in close partnership with Google to mitigate the Genisys threat, resulting in the removal of the identified fraudulent versions of these apps from the Play Store. Google Play Protect will warn users and automatically disable apps known to be associated with Genisys, even when they originate from sources outside of Google Play.
The scale of this infrastructure translated directly into advertiser exposure. Through coordinated background activity, the operation generated hundreds of millions of bid requests, injecting significant volumes of invalid supply into the programmatic ecosystem. Left undetected, activity of this kind can create financial risk, weaken marketplace integrity, and distort performance signals. IAS identified the coordinated patterns across domains, apps, and traffic behaviors and shared actionable intelligence with platform partners to enable disruption.
Genisys further obscured detection through extensive app bundle ID spoofing. Individual domains appear to receive traffic from hundreds of unrelated mobile apps, many with extremely large reported install bases. This manufactured attribution noise masked the set of apps generating the hidden activity, complicating enforcement and prolonging monetization.
GenAI-Created Laundering Domains
A defining feature of Genisys is the nature of the web domains loaded inside hidden in-app browser sessions.
In the Arcade operation, these domains were primarily gaming or entertainment focused. In Genisys, the IAS Threat Lab observed widespread use of domains created using GenAI tooling.
These sites typically present as blogs, news-style outlets, or general informational resources. When viewed at scale, clear patterns emerge:
- Highly similar layouts and navigation structures
- Repetitive content formats and article structures
- Minimal differentiation beyond domain names and superficial branding
Screenshots from a representative sample show that these domains are effectively interchangeable. Their purpose is not to attract readers or build an audience, but to exist as scalable endpoints for traffic monetization.
GenAI enables rapid production of such sites, allowing operators to rotate domains frequently and expand infrastructure faster than traditional detection methods can respond. IAS addresses this through pattern-level analysis across domains, apps, and traffic behaviors, identifying coordinated activity even as individual domains are replaced.
How the Genisys Threat Hid in Plain Sight
Genisys also introduces extensive app bundle ID spoofing as a core evasion tactic.
Traffic reaching Genisys domains is attributed to hundreds of distinct mobile apps. Many of the reported bundle IDs correspond to apps with tens or hundreds of millions of installs. This attribution is misleading.
Analysis shows that the bundle IDs do not reflect the apps actually generating the hidden in-app browser sessions. Instead, they are used to flood domains with implausibly diverse sources, creating attribution noise that makes it difficult to identify the true origin of traffic.
As a result, a single domain may appear to receive traffic from hundreds of unrelated apps, effectively masking the small set of apps actually responsible for the activity. This technique significantly reduces the effectiveness of attribution-based detection.
How the Operation Grew
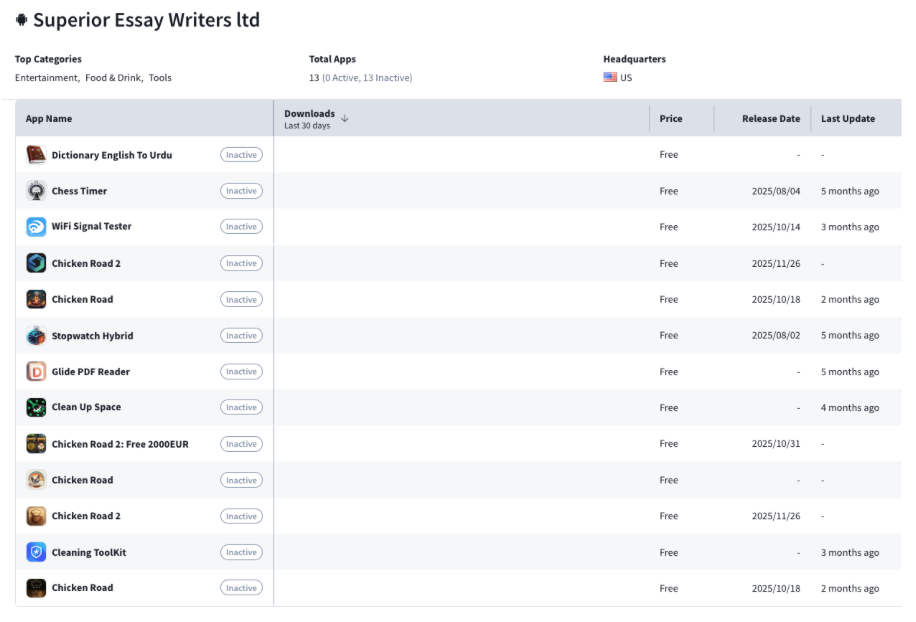
Of the mobile apps detected in Genisys, many are created by developers with a history of repeated abuse.
As an example, the IAS Threat Lab identified a developer account with 13 published apps, all of which have since been removed or rendered inactive. Multiple apps from this account exhibited traffic patterns consistent with the Genisys scheme prior to removal.
This pattern extends beyond a single developer. Apps are removed, but new apps continue to appear from the same developer profiles or associated entities. Developers publish low-effort apps at scale and monetize aggressively through background activity, allowing the broader operation to persist despite repeated enforcement actions.
Removing individual apps does not meaningfully disrupt operations when developers with extensive histories of violations are able to re-enter platforms.
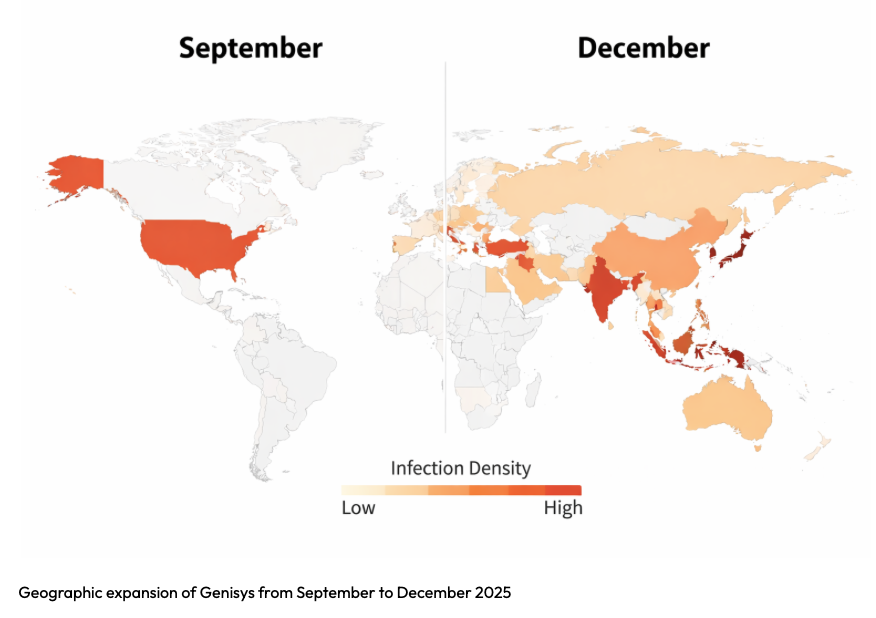
Distribution and Geographic Shifts
Genisys activity expanded geographically throughout Q4 2025. In September, the top affected regions were concentrated primarily in North America. By the end of the year, the top-10 composition consistently spanned APAC, LATAM, and EMEA, with 2–3 new countries entering each month from newly represented regions. This sustained increase in regional breadth, independent of total volume, indicates deliberate scaling across multiple markets rather than isolated spikes.
Taking Genisys Down
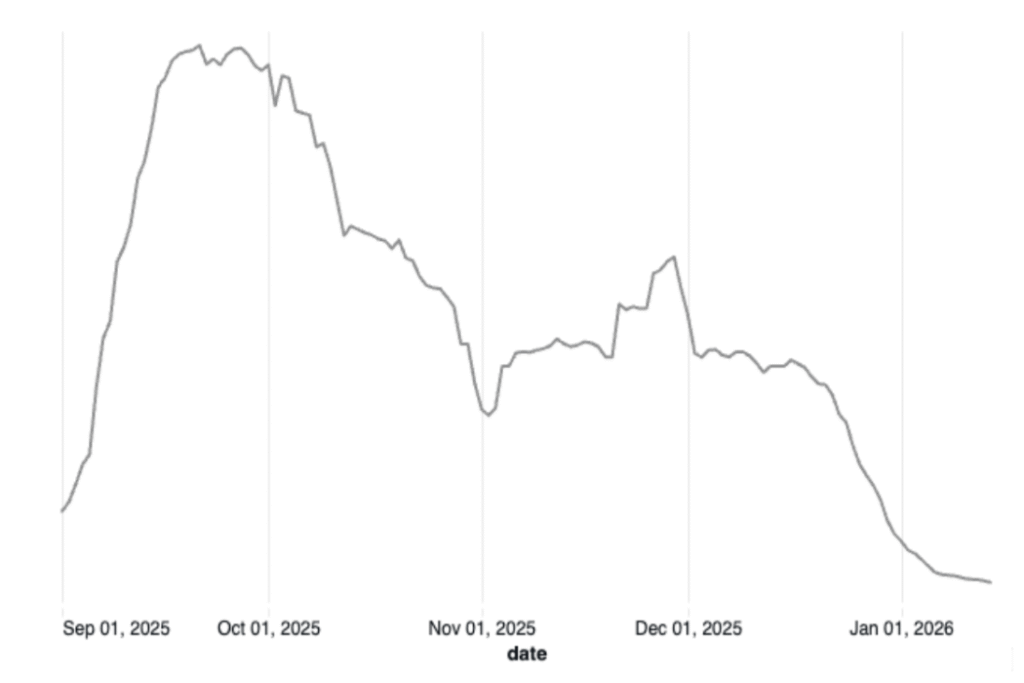
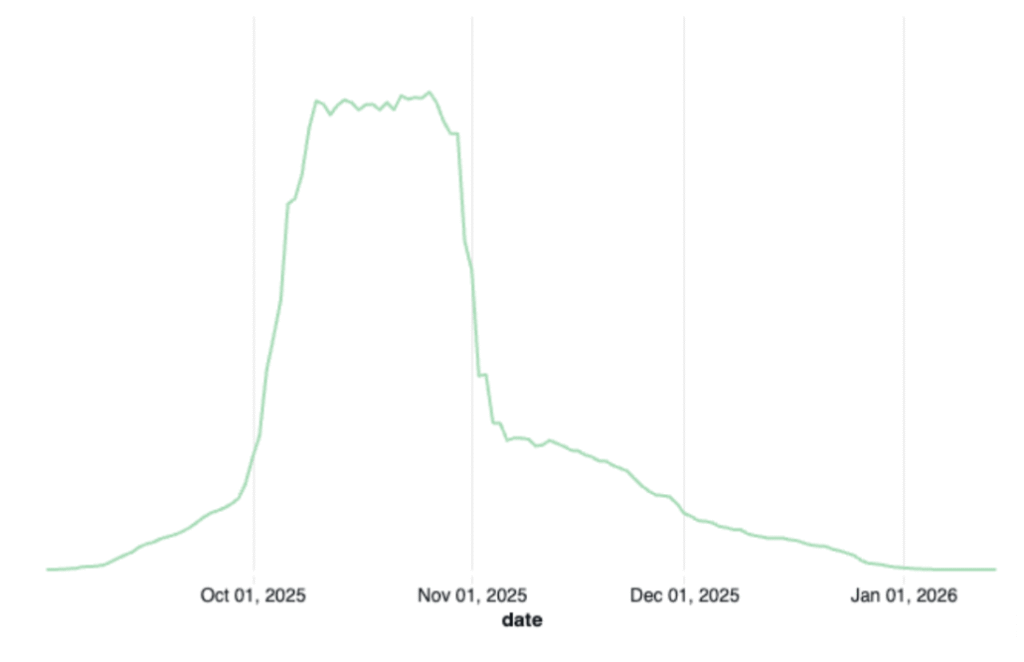
The IAS Threat Lab worked in close partnership with Google to disrupt the Genisys operation. After correlating anomalous traffic patterns and confirming the underlying mechanics, IAS shared actionable intelligence with Google’s Play Store team, which led to enforcement actions against the identified apps.
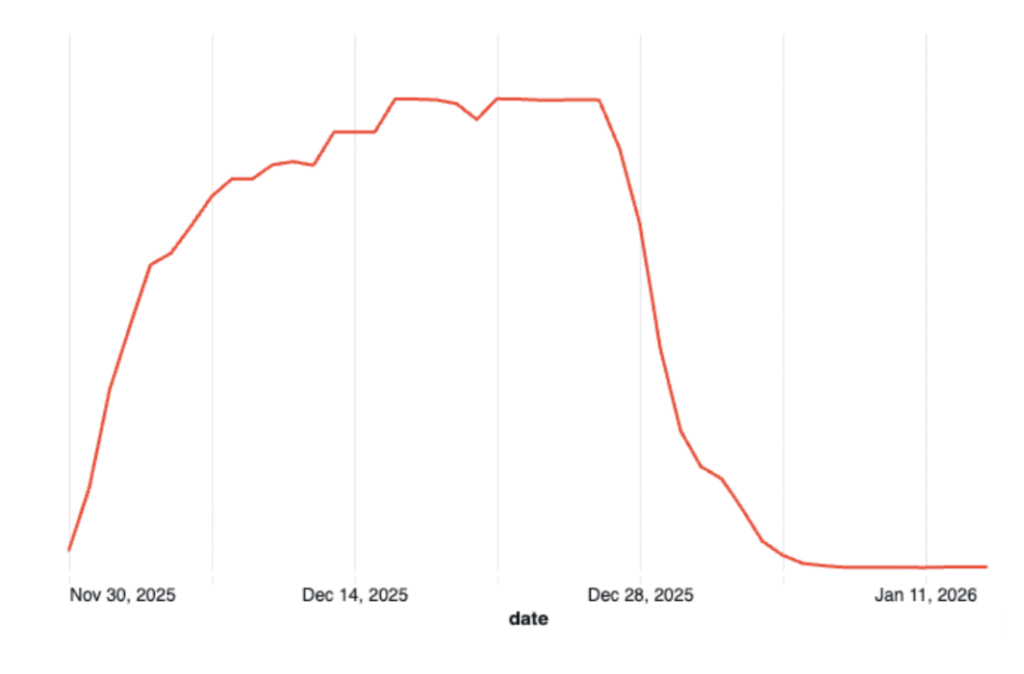
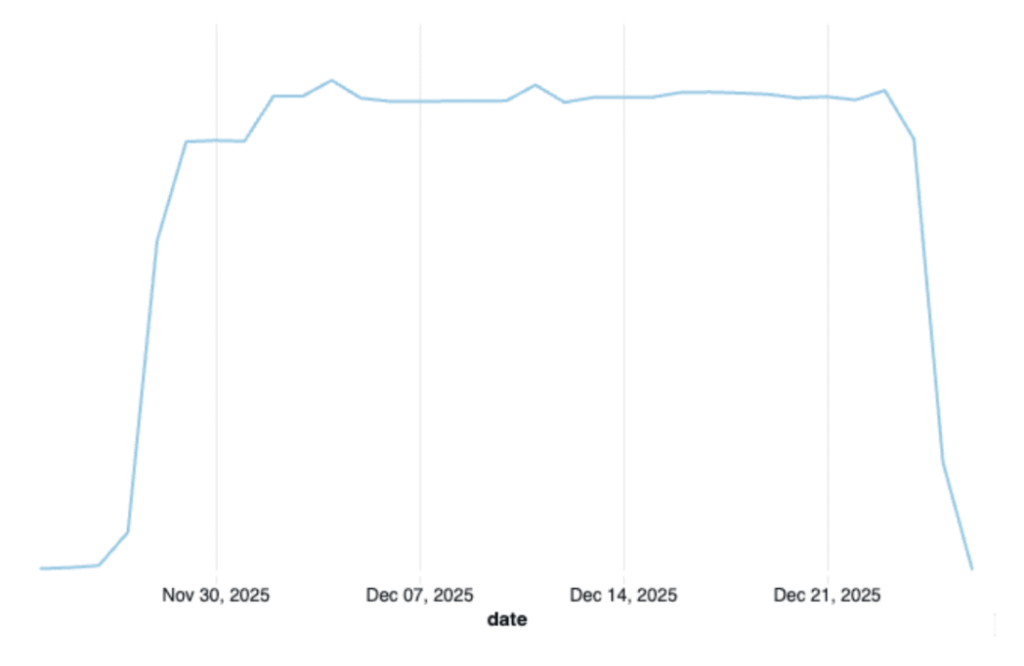
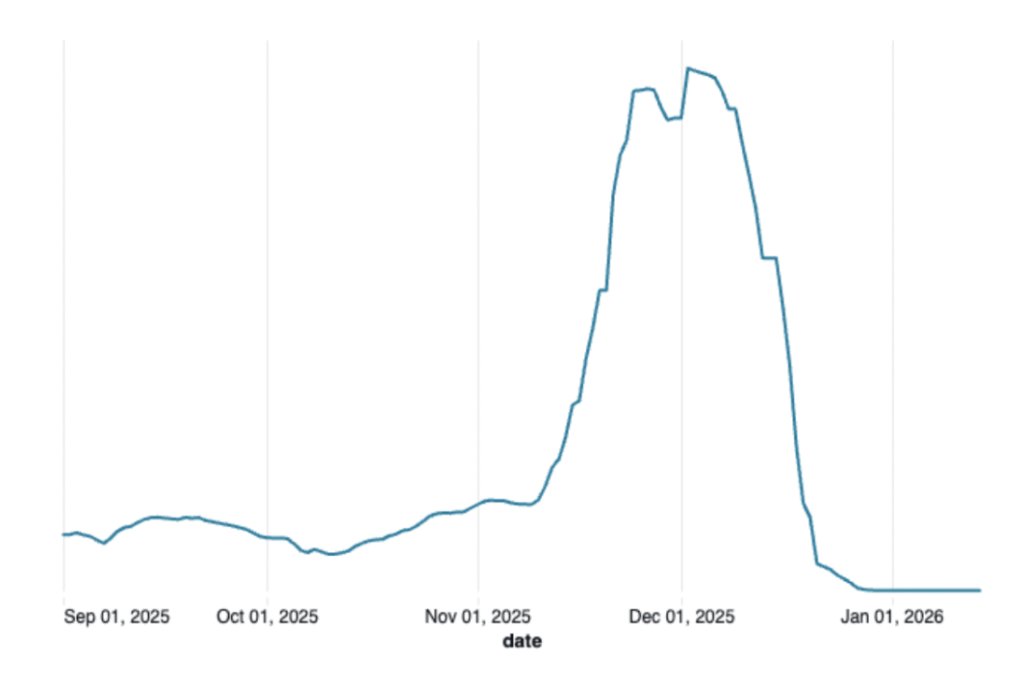
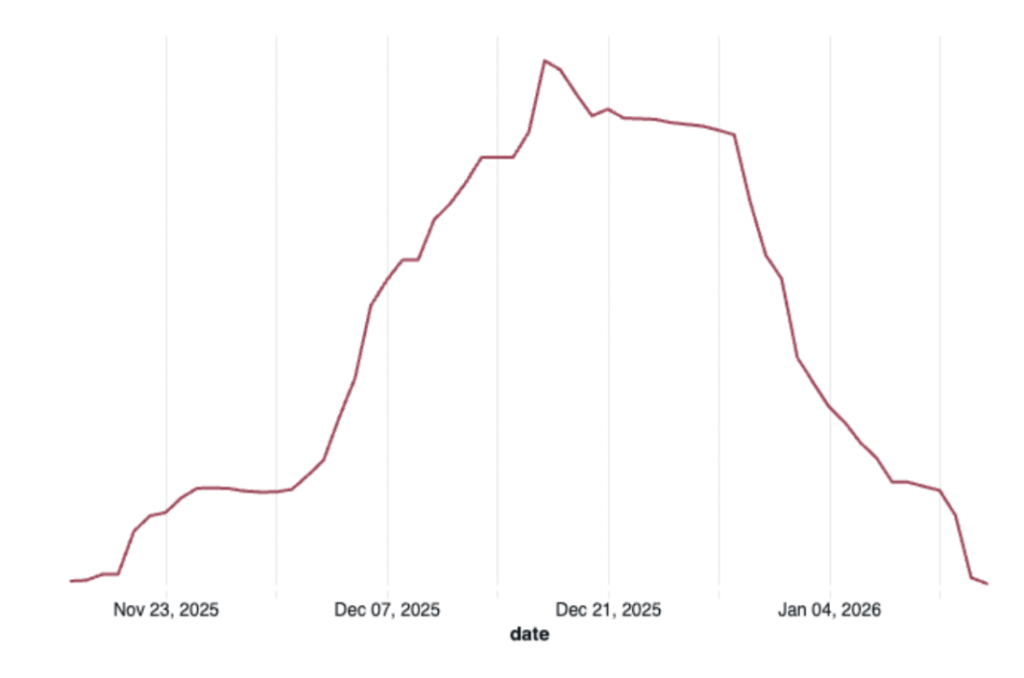
Following these enforcement actions, supply from affected apps declined sharply. As depicted below, for a representative set of Genisys apps, bid request volume dropped by more than 95% and has remained near zero since the removal of the identified apps.
These pronounced and simultaneous declines across multiple apps demonstrate the centralized nature of the operation and reinforce the value of coordinated intelligence sharing between IAS and platform partners.
The Shift in Large Scale Fraud Operations
Genisys reflects a broader shift in how large scale fraud operations are built and sustained.
Rather than relying on organic web properties, the operation is anchored in a synthetic ecosystem composed of hundreds of AI-generated domains designed specifically to receive and monetize app-generated traffic. This infrastructure is created quickly, rotated frequently, and scaled with minimal friction, allowing traffic laundering to persist even as individual components are removed.
The use of large scale app bundle ID spoofing further fragments attribution, enabling a limited set of apps to blend into a much larger and misleading source profile. Together, these tactics obscure the true origin of traffic, delay enforcement, and allow repeat offender developers to continue operating.
These changes reflect an intentional escalation in evasion tactics. Addressing schemes like Genisys requires coordinated enforcement that targets repeat offender developers, laundering domains, and monetization infrastructure together.
IAS Threat Lab remains committed to uncovering and disrupting evolving monetization schemes before they reach advertisers’ budgets.
Learn more about our AI-powered approach to combatting fraud pre- and post-bid.
 Share on LinkedIn
Share on LinkedIn Share on X
Share on X

