The IAS Threat Lab previously uncovered Arcade, a mobile ad fraud scheme in which apps generated hidden in-app browser activity to load websites in the background, converting mobile activity into web traffic without user awareness.
Following this discovery, continued monitoring revealed new traffic patterns and infrastructure that did not align with Arcade. This led to the identification of a distinct operation, now known as Genisys.
At its peak, Genisys operated at significant scale with nearly 500 AI-generated domains, embedding fraudulent activity directly within everyday smartphones and tablets across multiple markets. Devices were effectively hijacked to run background processes, consuming processing power and network resources without users’ knowledge or consent and without delivering any legitimate benefit.
⸻
A Synthetic Ecosystem Built with AI
A defining characteristic of Genisys is its reliance on a vast network of AI-generated web domains.
These domains typically appear as:
- Blog-style websites
- News-like platforms
- General informational pages
However, their purpose is not to attract genuine audiences. Instead, they are designed to receive and monetise fraudulent traffic generated by mobile apps.
At scale, clear patterns emerge:
- Nearly identical layouts and navigation structures
- Repetitive content formats
- Minimal differentiation beyond branding and domain names
Collectively, these sites form a synthetic web ecosystem, created to make illegitimate traffic appear credible within the programmatic advertising supply chain.
Unlike earlier schemes, Genisys leverages generative AI tools to rapidly produce and rotate domains, enabling operators to expand faster than traditional detection methods can respond.
⸻
Hidden Activity at Device Level
The fraud operated directly on users’ devices.
Compromised apps triggered hidden browser sessions in the background, generating activity without any visible interaction. This resulted in:
- Unauthorised use of device resources
- Artificial inflation of web traffic
- No value delivered to the user
From an advertiser perspective, this translated into large volumes of invalid supply entering the ecosystem.
⸻
Scale and Impact on Advertising
The scale of the operation had direct consequences for advertisers.
Through coordinated background activity, Genisys generated hundreds of millions of bid requests, introducing significant levels of invalid traffic into programmatic channels.
If left undetected, this type of activity can:
- Create financial risk
- Distort performance metrics
- Undermine trust in the marketplace
IAS identified coordinated patterns across apps, domains, and traffic behaviour, enabling disruption through collaboration with platform partners.
⸻
Evasion Through Attribution Manipulation
Genisys employed sophisticated evasion techniques, most notably app bundle ID spoofing.
Traffic directed to fraudulent domains appeared to originate from hundreds of unrelated mobile apps, many with very large reported install bases. In reality, this attribution was misleading.
Analysis showed that:
- The listed apps were not the true source of activity
- A small number of apps generated the traffic
- False attribution created significant “noise”, masking the origin
This made it far more difficult to detect and enforce against the operation.
⸻
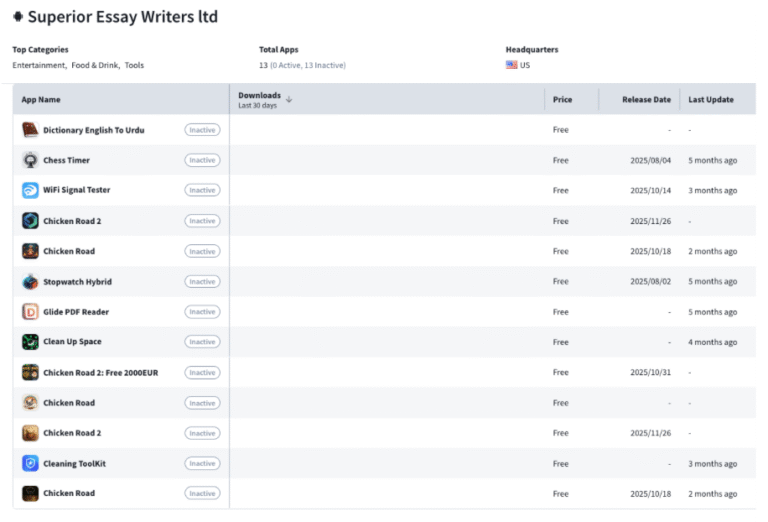
Persistent Developer Activity
The operation was sustained by developers with a history of repeated policy violations.
For example, IAS identified developer accounts publishing multiple apps, many of which were later removed, yet similar apps continued to reappear.
This pattern highlights a broader issue:
- Apps are removed
- New apps are quickly published
- The underlying operation continues
Without addressing repeat offenders at source, enforcement actions against individual apps have limited long-term impact.
⸻
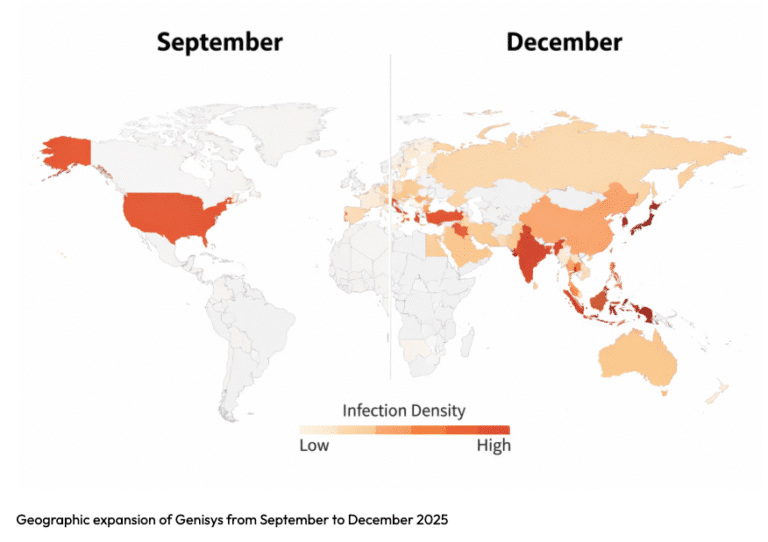
Global Expansion
Genisys activity expanded significantly during Q4 2025.
- Initially concentrated in North America
- Gradually spread across APAC, LATAM, and EMEA
- New countries were affected each month
This pattern suggests deliberate, coordinated scaling across regions, rather than isolated spikes in activity.
⸻
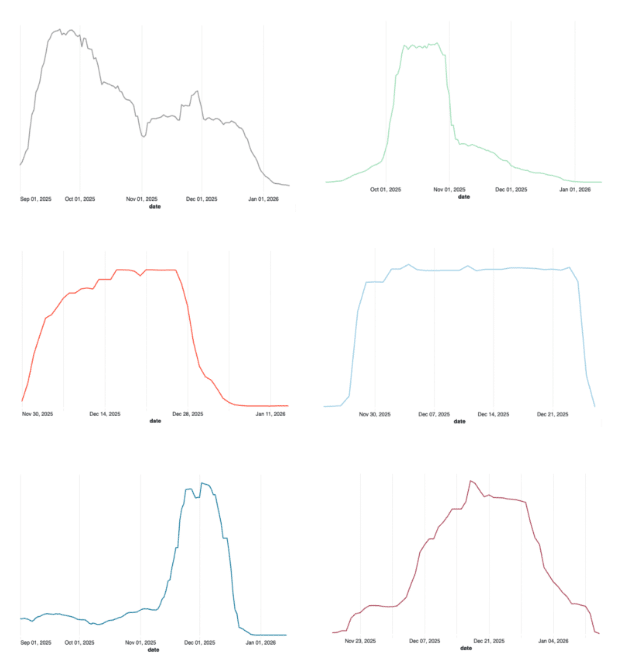
Disruption Through Collaboration
IAS Threat Lab worked closely with Google to disrupt the Genisys operation.
Following the sharing of detailed intelligence:
- Fraudulent apps were removed from the Google Play Store
- Google Play Protect began warning users and disabling affected apps even those installed official channels
As a result, traffic from affected apps dropped by more than 95%, demonstrating the effectiveness of coordinated enforcement.
⸻
A New Generation of Fraud Operations
Genisys reflects a broader shift in how large-scale ad fraud is designed.
Key characteristics include:
- AI-generated domain networks replacing traditional websites
- Rapid infrastructure creation and rotation
- Large-scale attribution spoofing to obscure origins
- Continued activity from repeat-offending developers
These tactics are specifically designed to:
- Delay detection
- Evade enforcement
- Sustain monetisation over time
⸻
Looking Ahead
Addressing operations like Genisys requires a coordinated, ecosystem-wide approach, targeting:
- Fraudulent apps
- AI-generated laundering domains
- Supporting monetisation infrastructure
IAS Threat Lab remains focused on identifying and disrupting evolving fraud schemes before they impact advertisers.
As digital environments continue to evolve, proactive detection, transparency, and collaboration will be essential to maintaining media quality and trust.
 Share on LinkedIn
Share on LinkedIn Share on X
Share on X


